Is Cryptocurrency Even Safe?
The potential of blockchain applications is endless. It is based on principles of cryptography, decentralization and consensus, which ensure trust in transactions. It eliminates the need for intermediaries in a wide array of transactions, virtually transforming every corner of the global economy.
Cryptocurrency, as a result of blockchain technology, gives us total control over our money, thereby becoming our own bank. On paper, crypto is generally safe thanks to the blockchain’s decentralized distributed ledger and the encryption process every transaction undergoes.
However, the crypto space is still in development, and most of us still have to rely on third-party wallet providers to store our crypto. The security of our fund is only as safe as the safeguards and security measures the provider has in place.
As crypto evolves, so do hackers and scammers. Malicious actors are getting more creative at exploiting vulnerabilities in blockchain projects, devising new tactics to bypass their security controls.
How Much Money Has Been Stolen to Date?
Over the years, hackers have exploited loopholes within the platforms of these third parties, especially on DeFi protocols. They have also coordinated attacks on certain cryptocurrencies directly such as utilizing flash loans to their advantage — borrowing a large amount of funds without collateral to quickly carry out pump-and-dump schemes.
To this date, more than $7 billion have been stolen in the crypto space. As crypto prices tend to change, that $7 billion would be worth so much more today. If the hackers were to cash it in today, they would have amassed a fortune worth more than $40 billion!
This number alone is from exploits and thefts by hackers. It does not include other events such as rug pulls or corporate fraud. Those numbers would be even higher if they are added together.
Five Largest Crypto Hacks in History
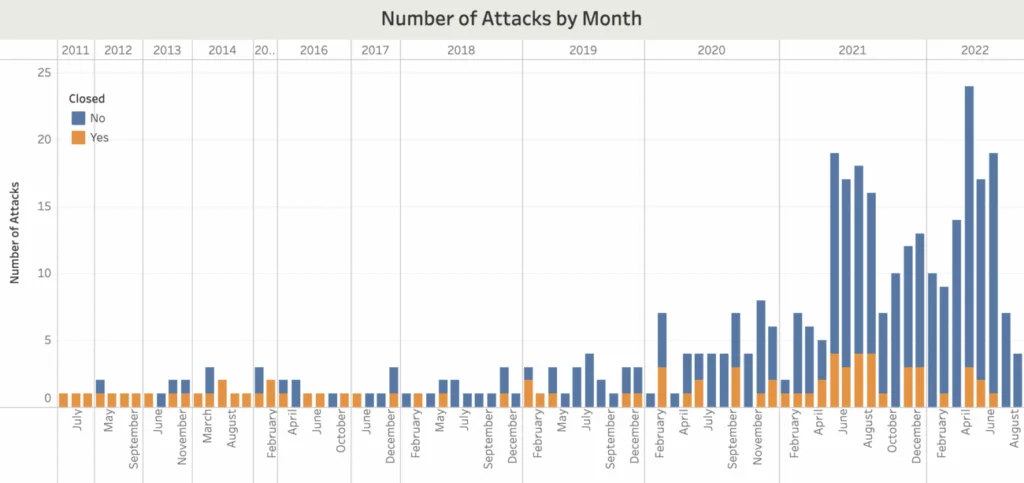
Comparitech, a pro-consumer website that focuses on cyber security, has managed to track and record all attacks that have happened in the crypto space since 2011.
There are 365 recorded attacks so far and the five largest hacks make up more than one-third of the stolen $7+ billion:
Ronin Network (Axie Infinity) – $620 Million Stolen
Ronin Network is an Ethereum-linked sidechain that powers Axie Infinity, one of the leading blockchain games. On 29 March 2022, Ronin Network was hacked and 173,600 ETH and 255,000 USDC were stolen as a result, worth $620 million at the time.
The U.S. Treasury Department attributed the hack to Lazarus, a North Korean hacking group. Lazarus reportedly reached out to developers of Axie Infinity via LinkedIn on the pretense of a fake company, offering them an “extremely generous” compensation package.
A senior engineer took the bait and clicked a PDF which supposedly contained the “offer.” This led to the engineer’s computer being compromised as well as the validator nodes of the Ronin Network.
Poly Network – $610 Million Stolen
Poly Network is a cross-chain protocol that implements blockchain interoperability in DeFi. In August 2021, a hacker managed to exploit a vulnerability in Poly Network’s code which enabled them to transfer more than $600 million worth of tokens to their own account.
Through a series of negotiation, Poly Network pleaded with the hacker to return the stolen funds, calling him “Mr. White Hat.” The platform even offered him a $500,000 bounty and a job as “chief security advisor.” Surprisingly, the hacker returned all of the stolen funds!
Security experts believe that it was likely the hacker realized it would be impossible to launder the money and cash out, since all transactions are recorded on the blockchain.
Coincheck – $532 Million Stolen
Coincheck is a Japanese cryptocurrency exchange and NFT marketplace founded in 2012. In January 2018, its NEM (XEM) tokens worth more than $530 million at the time were stolen and transferred to 11 different addresses.
Hackers exploited the fact that the tokens were being stored in a “hot wallet”, which was connected to the server. This made it susceptible to phishing attacks.
Coincheck also did not have a multi-signature security measure in place, which requires more than one person to sign off before funds can be moved. As a result, a single point of failure would be established.
MT Gox – $470 Million Stolen
MT Gox was a Japanese Bitcoin exchange founded in 2010, and it was handling over 70% of all Bitcoin transactions worldwide by early 2014.
It is arguably the most infamous case of crypto hacks in history. It was the first large-scale hack on an exchange and is still the biggest theft of Bitcoin (BTC) from an exchange to this day.
The attack on MT Gox was not a solitary event. Rather, the exchange had been leaking funds since 2011, until it was discovered in February 2014. During this period, around 100,000 BTC were stolen from the exchange and 750,000 BTC were stolen from the exchange’s customers. At the time, these BTC were both $470 million, but today, they are worth around $4.7 billion!
MT Gox filed for bankruptcy shortly after the hack. Only 200,000 of the stolen BTC were successfully recovered.
Wormhole – $326 Million Stolen
Wormhole is a blockchain bridge between Solana and other top DeFi networks, allowing users to swap Solana tokens (SOL) for other crypto on DApps across the Ethereum network.
The attack exploited a signature verification vulnerability in the network that allowed the hacker to freely mint 120,000 wrapped ETH (wETH), worth $326 million at the time.
Cross-chain bridges are critical infrastructure in the DeFi ecosystem as users can move their funds between blockchains. A lot of money is being moved. This means that security is a number one priority for these platforms. However, Wormhole was harshly criticized for its lack of comprehensive security audit before going live.
According to an article by Hacken, though Solana may be blamed for providing the instrument with security flaws to its projects, Wormhole might have “prevented the incident by auditing the instruments it used.”
The Bottom Line
Despite improvements, the crypto industry still faces security concerns, especially in peer-to-peer ecosystems where anybody can join anonymously. It becomes almost impossible to track malicious actors when their identity is hidden.
New forms of cyber threats are emerging that are capable of causing massive, irreparable damage. And this list will only continue to grow unless there is a solid security measure that is widely established.
Therefore, it is important to learn about the potential security flaws that are prevalent in third-party platforms like DeFi, crypto wallets and exchanges. As investors, we should recognize the kinds of attacks that hackers pull off so that we can spot and avoid them beforehand.

ronalthapa
Ron achieved $60,000+ (peak PnL) in airdrop rewards in 2024. He is an expert in testnet airdrop farming. If there is a points system, he knows exactly how to min-max it. Ron is also a data-driven trader, proficient in LTF price action. He hopes one day to be in the top 10 of the Bybit WSOT leaderboard.
